- A TechNote on Wireless and Mobility
- Joanie M. Wexler
- Technology Analyst/Editor
- Editorial Director, TechNotes
Call it a chicken-and-egg situation, a Catch-22, a vicious circle or any of your other favorite clichés. I'm talking about Android's prospects for success in the enterprise.
Popular with Consumers; Anathema to IT
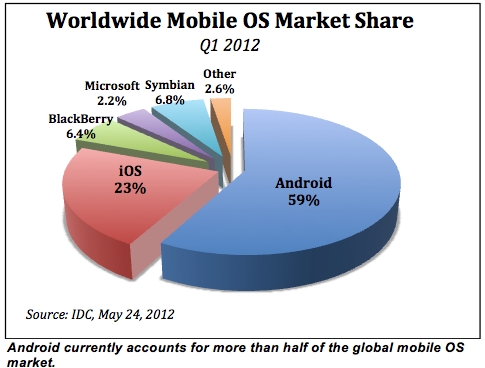 To say that Android-based devices are popular with consumers is an understatement. IDC estimates that Android claimed 59% of the mobile OS market worldwide during the first quarter of this year, for example (see figure), and comScore MobiLens calculates that the OS garnered about 51% share in the U.S. during the same time period.
To say that Android-based devices are popular with consumers is an understatement. IDC estimates that Android claimed 59% of the mobile OS market worldwide during the first quarter of this year, for example (see figure), and comScore MobiLens calculates that the OS garnered about 51% share in the U.S. during the same time period.But Android has been struggling in the enterprise. And by "struggling" I mean that most enterprises haven't sanctioned Android smartphones and tablets as corporate-owned and managed devices, the way they welcomed BlackBerry in the past and, increasingly, are embracing Apple iOS devices. Why?
- Bad security rep. Android is known as a favorite target of mobile hackers; it's "openness" gives users more freedom but also breeds familiarity with the OS's vulnerabilities. Also, the Android app vetting process is not as stringent as others', so harmful applications are more likely to make their way onto Android devices than others.
- Fragmentation. There are so many versions of Android implemented in different ways, it's complex for enterprises to manage the OS. Mobile device makers tend to release new handset and tablet form factors for multiple concurrent versions of the Android OS. Aside from being confusing for users, this situation creates a management nightmare and issues for software developers trying to support the various versions. In a corporate-liable world, enterprises could standardize on one or two manufacturers and Android versions. But in a BYOD world, the choice of handset model and Android version rests with the user.
- Scarcity of application programming interfaces (APIs) and enterprise policies. The APIs and policies supported haven't held a candle to what enterprises came to expect with BlackBerry and, increasingly, are getting from the iOS platform.
Enterprise-Readiness: What's Being Done
In anticipation of Android's inevitable but potentially unwelcome arrival in the enterprise, there are a few developments afoot. To some degree, the device manufacturers themselves are taking it upon themselves to get Android into enterprise-ready shape.
For example, Samsung, whose Galaxy S III debuted in the U.S. this week with AT&T, Sprint, T-Mobile USA, Verizon Wireless and U.S. Cellular, has created more than 700 APIs and 300 enterprise policies for its Galaxy platform. These can be implemented in mobile device management (MDM) solutions from Samsung partners such as MobileIron and Sybase/Afaria/SAP and compare with just 30 to 35 default Android APIs offered natively by Android's creator, Google.
For its part, Google recently completed its acquisition of mobile device maker Motorola Mobility, which could result in extra enterprise goodies in those devices. In addition, Motorola Mobility had acquired 3LM, a maker of MDM and mobile applications management and security, in early 2011 and has licensed the enterprise technology to other device makers such as HTC, Pantech, Sharp and Sony Ericsson. So there's hope for those hardware platforms, as well.
And on the security front, in February of this year, Google made known the existence of "Bouncer," a service that automatically scans apps introduced to its Google Play app store (formerly the Android Market) in search of malicious software. Hiroshi Lockheimer, VP of engineering for Android at Google, wrote in a blog at that time that thanks to the malware detection/prevention capabilities, "between the first and second halves of 2011, we saw a 40% decrease in the number of potentially-malicious downloads from Android Market."
On the other hand, reports surfaced just this week that Bouncer is far from foolproof and that it is undergoing some work with security experts to plug the gaps.
Wi-Fi vendors are deploying network access control (NAC) for mobile devices, which will filter access requests from devices. Many of them, too, are teaming with MDM vendors to unite their respective capabilities. And the MDM vendors themselves are poised to launch mobile app security capabilities intended to work across any flavor of Android OS and any Android device to ease the fragmentation issue. Announcements will come as early as this week.
This TechNote is brought to you in part due to the generous support of:











Joanie, you hit the nail on the head: risk, fragmentation, and immature IT controls.
By the way, Android market fragmentation affects a lot more than just security - device diversity makes it harder to develop enterprise apps that perform consistently and reliably (despite platform openness), and it also makes it harder for help desks to deliver uniform support. Manufacturer APIs help in one way by enabling deeper/broader IT control, but they also increase diversity, forcing developers to develop and maintain customizations for each supported OEM. This is going to be a tug-o-war for quite some time, I'm afraid.
One observation about Google Bouncer: a post-publication anti-malware scanner isn't the same as pre-publication code review. Post-publication scans are clearly valuable - that's why we all run A/V on our laptops and servers. But complementing Bouncer with pre-publication code review and banning publication of self-signed apps would create a stronger deterrent. Also, scanning Google Play for malware is like frisking visitors who pass through a front door while leaving a side door wide open - it's not enough to prevent malware from being side-loaded from other sources.