- A TechNote on Wireless and Mobility
- Lisa Phifer, President
- Core Competence, Inc.
Ever since 802.11 found its way into the workplace, wireless intrusion prevention systems (WIPS) have been a security best practice for enterprise WLANs. But nearly a decade later, WIPS adoption still hovers around 26%. Why? Mid-size and small businesses often lack the funds or expertise to deploy their own WIPS, or simply don't find the risk/reward compelling enough.
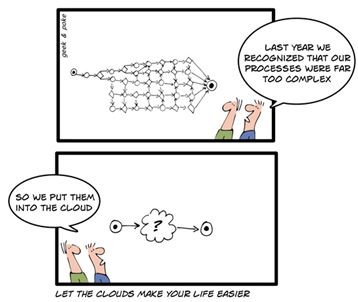
To fill this gap, vendors such as AirTight Networks, Motorola Solutions, and Meraki have started to offer WIPS as cloud service. Let's take a look at how cloud deployment can make WIPS more affordable, especially for SMBs.
Tapping cloud potential
 Like traditional on-premise WIPS, a cloud WIPS still observes traffic with listening devices -- sensors or APs -- deployed throughout the airspace to be protected. But with a cloud WIPS, those sensors/APs report what they hear to an Internet-accessible WIPS server running on a multi-tenant or dedicated cloud computing platform owned and maintained by a service provider. This approach significantly reduces initial deployment time and capital expense, letting customers learn about WIPS while paying only for services actually used.
Like traditional on-premise WIPS, a cloud WIPS still observes traffic with listening devices -- sensors or APs -- deployed throughout the airspace to be protected. But with a cloud WIPS, those sensors/APs report what they hear to an Internet-accessible WIPS server running on a multi-tenant or dedicated cloud computing platform owned and maintained by a service provider. This approach significantly reduces initial deployment time and capital expense, letting customers learn about WIPS while paying only for services actually used.These attributes appealed to Senior Manager of Information Security Lazaro Corrales when Citrix Systems went with AirTight Cloud Services two years ago.
"Before we brought in AirTight's cloud offering, we compared it to on-premise solutions. When we looked at price points and support, the case was overwhelmingly weighted towards cloud WIPS," he said. "Today, we have deployed hundreds of sensors globally. We are now entering our second phase, making cloud WIPS a standard for all of our offices."
Cloud WIPS is a pay-as-you-go offering, with service fees based on feature set and the number of (purchased or rented) sensors/APs. While this reduces up-front investment, those recurring fees add up over time. "At a certain point, cloud WIPS seemed like it could become more expensive, but not when we factored in the FTEs required to maintain on-premise WIPS," said Lazaro. "That OpEx reduction was actually more attractive to us than CapEx savings."
Grow as you go
Cloud WIPS also scales. Customers can direct-ship sensors or APs as needed to new remote offices that require monitoring. Anyone can plug those zero-touch devices into a LAN with Internet access; no on-site configuration is needed. Sensors/APs automatically connect to the provider's cloud server, where they get remotely provisioned with customer-defined scanning and prevention rules.
"Ease of deployment was a big deal for us - we were able to grab and deploy [a WIPS sensor]; it would immediately show up on our console and off we'd go. When it comes to scaling, [cloud WIPS] is great because all I have to do is plug in [new sensors] and the solution will keep scaling. I don't have to consider upgrading servers as I would in an on-premise WIPS," explained Lazaro.
Cloud WIPS also offers flexibility. Once sensors/APs are installed, adding features can be as simple as logging into a cloud WIPS portal and activating a service option. For example, AirTight customers can start with basic intrusion detection and reporting (e.g., to satisfy PCI DSS requirements), stepping up to proactive prevention and rogue containment when and where needed. Cloud WIPS services can also offer features that go beyond security, such as WLAN health and performance monitoring.
Delegation and trust
Cloud WIPS may simplify deployment, but there can still be operating challenges. Whether a WIPS runs on-premises or in-the-cloud, the underlying engine must accurately detect, locate and classify intruders. And even though the provider maintains the platform itself - updating software, storing massive volumes of collected data - customers are still responsible for defining their own WIPS policies and deploying enough sensors/APs to enable effective execution.
In fact, customers that opt for cloud WIPS are entering into a partnership with their WIPS service provider. As with an on-premises WIPS, it is important to choose a cloud WIPS platform that reliably meets your business' needs. In addition, consider how the service itself is secured and supported. How does the provider control WIPS console access? What steps are taken to prevent data breach, corruption or loss, ensure high availability, and support role-based operator access to WIPS alerts, reports, commands and policies?
In Lazaro's experience, trusting a cloud WIPS is not really that different than outsourcing other hosted services. "We have to be able to adapt and take advantage of the benefits that cloud solutions can bring to our business," he said. "But not all cloud services are created equally; we have to leverage independent audits and certifications. As long as you have confidence in [the provider] you're working with and [the underlying WIPS platform's] maturity, you can have reasonable expectations that your cloud WIPS is going to be secure."











Cisco's acquisition of Meraki yesterday is a validation of both cloud-based WIPS and WLAN management. Meraki is a relative newcomer to cloud WIPS, but has long focused on cloud management.
For an apples-to-apples comparison of cloud managed WLAN offerings (including AirTight, Meraki, and Motorola, all mentioned in this cloud WIPS TechNote), read my InformationWeek report: http://reports.informationweek.com/abstract/18/9005/Mobility-Wireless/research-cloud-managed-wlan-buyer-s-guide.html